Cloud infrastructure has evolved into a highly dynamic and distributed system where resources are created, modified, and destroyed continuously. Organizations no longer operate within clearly defined perimeters; instead, they manage ecosystems composed of microservices, APIs, managed services, and identity-driven access layers across multiple cloud providers.
This shift has fundamentally changed the nature of security risk. In traditional environments, breaches were often the result of external attacks targeting known vulnerabilities. In cloud-native systems, however, risk increasingly originates from within—through misconfigurations, excessive permissions, and inconsistent policy enforcement. These issues are not edge cases but systemic outcomes of operating at scale in complex environments. Cloud providers themselves highlight that configuration errors remain one of the leading causes of security incidents in modern architectures.
As infrastructure becomes programmable and deployment cycles accelerate, the ability to manually audit and validate configurations disappears. Security teams can no longer rely on periodic reviews or static controls to ensure systems remain secure over time.
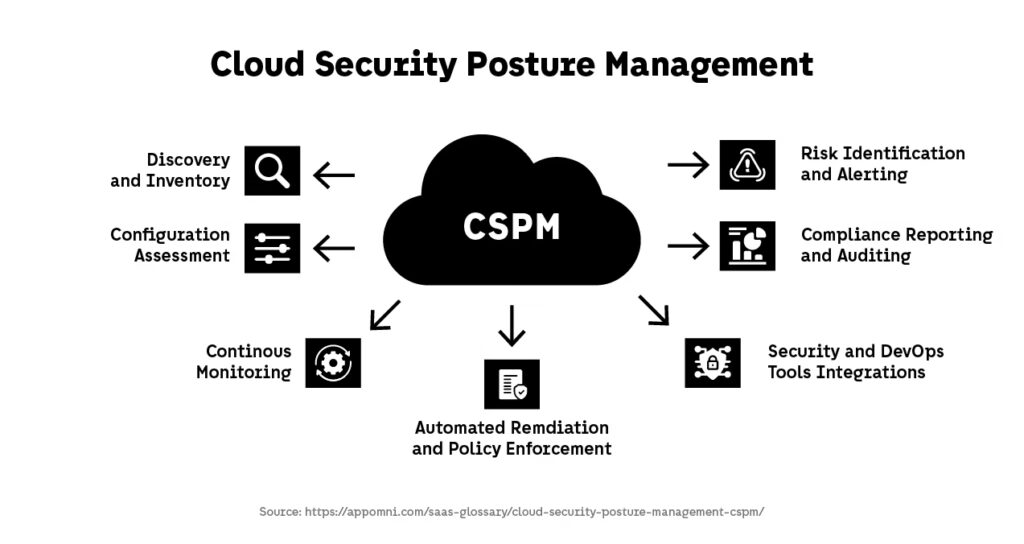
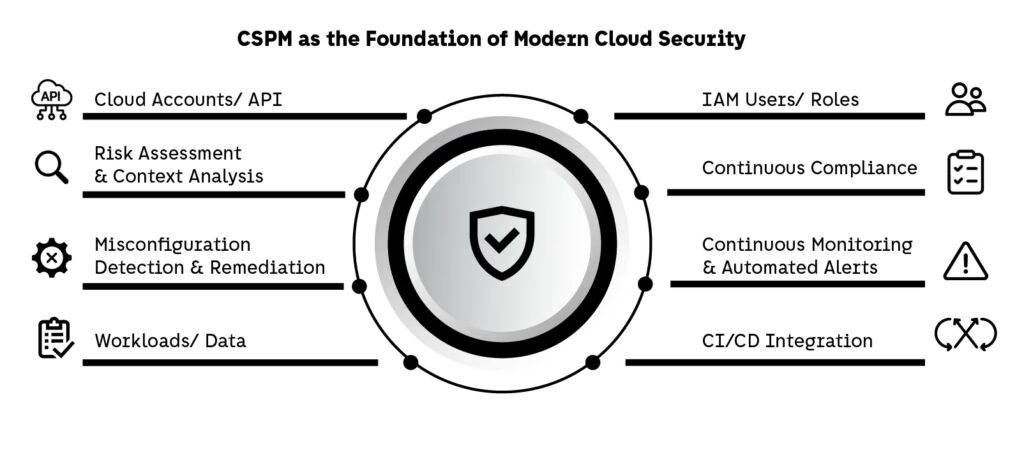
Cloud Security Posture Management (CSPM) emerges as a response to this structural challenge. Rather than focusing on detecting attacks after they occur, CSPM introduces a continuous validation layer that ensures cloud environments remain aligned with security best practices, compliance requirements, and internal policies.
In this article, we examine CSPM as an architectural capability: how it works, why it has become essential in 2026, and how it integrates into modern cloud-native and DevSecOps ecosystems.
What Is Cloud Security Posture Management (CSPM)
Understanding CSPM as a Continuous State Validation Layer
Cloud Security Posture Management (CSPM) is not simply a category of security tooling—it is a continuous validation layer embedded within cloud environments to ensure that infrastructure remains in a secure and compliant state over time.
At its core, Cloud Security Posture Management answers a fundamental question: Is the current state of the system aligned with what is considered secure?
This involves continuously evaluating cloud resources against a defined set of rules derived from:
- cloud provider best practices
- regulatory and compliance frameworks
- internal security policies
- architectural standards
Unlike traditional security approaches that focus on detecting known vulnerabilities or active threats, Cloud Security Posture Management operates at the configuration level. It inspects how systems are built and interconnected rather than waiting for malicious behavior to surface.
This distinction is critical because, in cloud environments, security failures are often not the result of sophisticated attacks, but of simple configuration errors that expose systems unintentionally.
These capabilities form the foundation of CSPM, but their importance becomes clearer when we examine how configuration itself evolves into the primary source of risk in cloud environments.
Why Configuration Becomes the Primary Attack Surface
In cloud-native architectures, infrastructure is defined and deployed through code. This introduces a level of speed and repeatability that fundamentally changes how risk propagates.
A misconfigured resource is no longer an isolated issue. It can be:
- replicated across environments through shared modules
- deployed automatically through CI/CD pipelines
- left undetected due to lack of centralized visibility
For example, an overly permissive IAM role defined in a reusable infrastructure module can silently propagate across dozens of services. Each instance increases the potential attack surface without introducing any obvious failure signal.
This is why configuration becomes the dominant risk vector. It is embedded in the system itself, not introduced externally.
CSPM addresses this by continuously:
- scanning deployed infrastructure
- identifying deviations from expected configurations
- correlating risks across resources and environments
This transforms security from reactive investigation into proactive system validation.
CSPM and the Shift to Identity-Driven Security Models
Modern cloud systems are not secured by network boundaries—they are governed by identity and access control.
Every interaction between services is mediated through:
- roles
- permissions
- service accounts
- policies
This makes identity the primary enforcement layer of security.
CSPM plays a critical role in this model by analyzing identity configurations at scale. It can detect:
- excessive permissions that violate least privilege principles
- unused or orphaned credentials
- privilege escalation paths across services
These issues are particularly dangerous because they enable lateral movement within systems once an initial foothold is established.
The broader shift toward identity-centric security is formalized in Zero Trust architecture, where trust is continuously evaluated rather than implicitly granted.
Cloud Security Posture Management operationalizes this principle by ensuring that identity configurations remain constrained, observable, and aligned with security intent.
How Cloud Security Posture Management Works in Practice
Continuous Discovery and Asset Contextualization
CSPM begins with continuous discovery of all resources deployed across cloud environments. This is not a one-time inventory but a real-time process that reflects the dynamic nature of modern systems.
In cloud-native architectures, resources are constantly created and destroyed through automated pipelines, scaling mechanisms, and ephemeral workloads. This includes not only compute instances and storage services, but also identities, permissions, network rules, and service relationships.
CSPM platforms integrate directly with cloud provider APIs to build a live map of:
- infrastructure components
- identity relationships
- network exposure paths
- data flows between services
This contextual layer is critical. A misconfiguration is only meaningful when understood in relation to what it exposes. A publicly accessible resource, for example, may represent low risk in isolation but become critical when connected to sensitive data or privileged identities.
Without continuous discovery and context, security visibility is incomplete and decisions are based on partial information.
Policy Evaluation and Risk Detection at Scale
Once the environment is mapped, Cloud Security Posture Management continuously evaluates resources against a set of policies and security rules.
These policies are derived from:
- industry benchmarks (CIS, NIST)
- cloud provider best practices
- internal governance models
Each resource is assessed to determine whether it complies with expected configurations. This includes checks such as:
- whether storage is publicly accessible
- whether encryption is enabled
- whether IAM roles follow least privilege principles
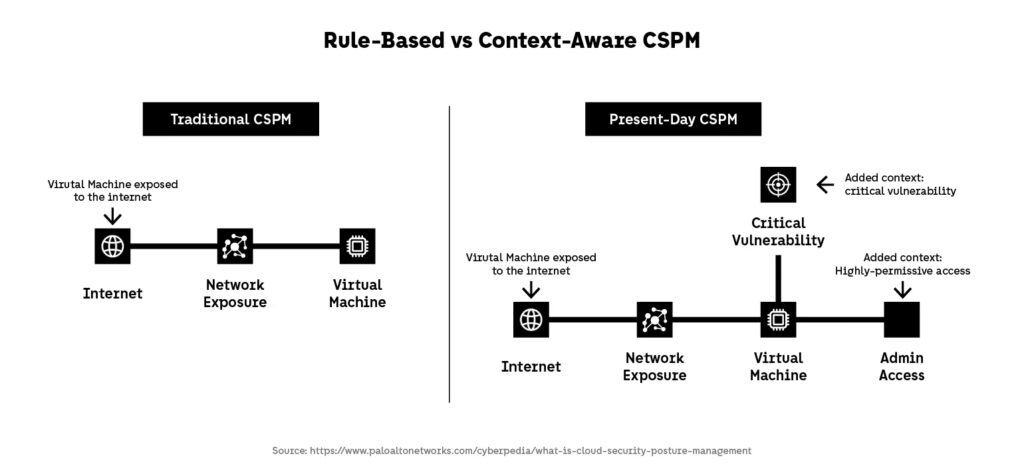
However, modern Cloud Security Posture Management systems go beyond simple rule matching. They incorporate context-aware analysis to prioritize risk based on:
- resource criticality
- exposure level
- relationships between services
- potential attack paths
This allows organizations to move away from binary “pass/fail” assessments toward a more meaningful understanding of actual risk.
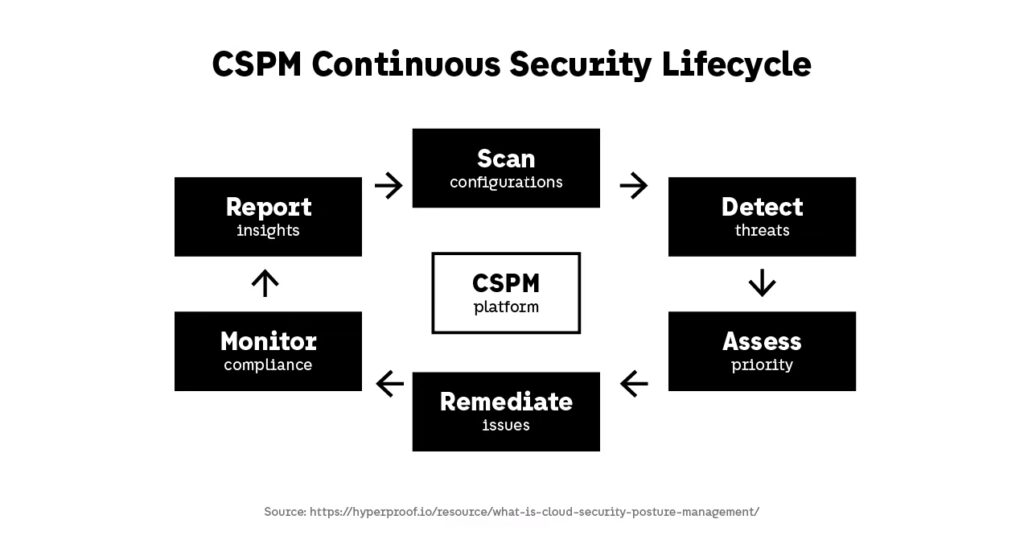
This continuous loop reflects how CSPM operates as an active system rather than a static control, ensuring that security posture evolves alongside the infrastructure itself.
CSPM in Multi-Cloud and Kubernetes Environments
The Complexity of Multi-Cloud Environments
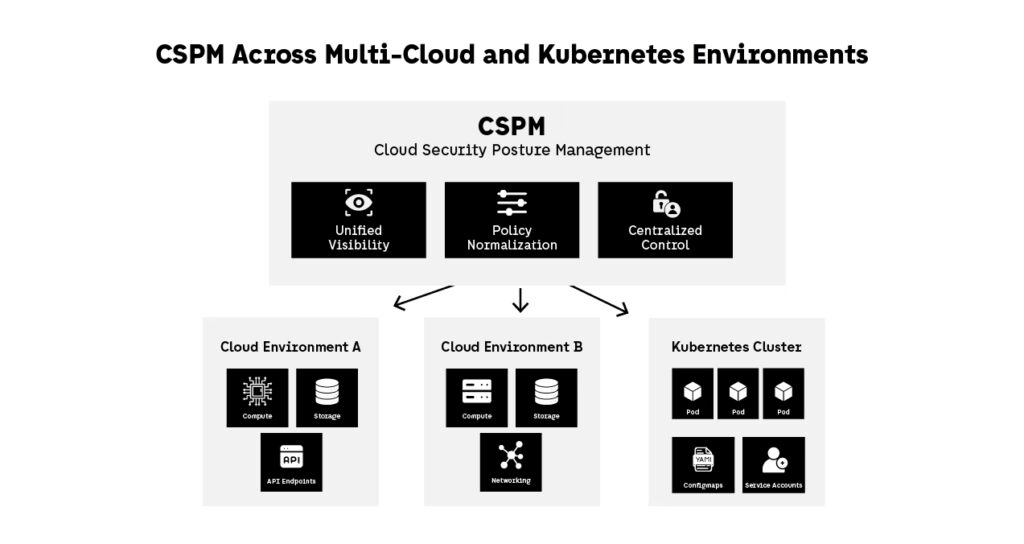
Modern organizations rarely operate within a single cloud provider. Instead, they adopt multi-cloud strategies to improve resilience, avoid vendor lock-in, and optimize workloads across different platforms.
While this approach increases flexibility, it also introduces structural complexity. Each cloud provider defines its own identity models, networking abstractions, and configuration standards, making it difficult to enforce consistent security policies across environments.
This fragmentation creates a new category of risk. Security is no longer confined to a single platform but distributed across interconnected systems, where inconsistencies between environments become potential attack surfaces.
Cloud Security Posture Management (CSPM) addresses this challenge by introducing a unifying layer of visibility and control. It enables organizations to standardize policies, monitor configurations centrally, and reduce the risks introduced by multi-cloud fragmentation.
For a deeper technical perspective on multi-cloud security challenges, see Google’s architecture guidance.
Kubernetes and Ephemeral Infrastructure
Kubernetes amplifies the complexity of cloud-native environments by introducing a dynamic, highly abstracted execution model. Workloads are no longer tied to specific machines; they are scheduled, scaled, and replaced continuously based on system demands.
This creates a security model where:
- resources are short-lived and constantly changing
- configurations are distributed across multiple layers
- service-to-service communication is dynamic and often internal
Misconfigurations in Kubernetes environments are rarely isolated. A single issue—such as an overly permissive role binding or an exposed service—can affect multiple workloads and propagate across clusters.
Cloud Security Posture Management extends into this domain by integrating with Kubernetes environments to analyze configurations at different levels, including:
- cluster-level security settings
- namespace isolation and permissions
- workload-level configurations and exposure
In this context, CSPM must move beyond static configuration checks and incorporate awareness of relationships between workloads, identities, and runtime behavior.
Identity as the New Security Perimeter
One of the most significant shifts in cloud-native architecture is the move from network-based security to identity-driven security.
In traditional systems, access was controlled by network boundaries. In cloud environments, access is defined by identities and permissions:
- roles assigned to users and services
- service accounts used for internal communication
- policies governing API access
This makes identity the primary enforcement layer of security.
Cloud Security Posture Management plays a critical role in this model by continuously evaluating identity configurations. It helps identify:
- excessive permissions that violate least privilege principles
- unused or orphaned credentials
- potential privilege escalation paths
This approach aligns with Zero Trust principles, where trust is continuously evaluated based on identity and context rather than location.
Managing Risk Across Distributed Systems
As cloud systems become more distributed, risk is no longer defined by individual components but by the relationships between them.
A configuration that appears secure in isolation can become a critical vulnerability when combined with other elements in the system. For example:
- a publicly exposed API
- connected to a backend service with elevated permissions
- accessing sensitive data
Individually, each component may appear acceptable. Together, they form a high-risk attack path.
Cloud Security Posture Management enables organizations to detect these compound risks by:
- mapping relationships between resources
- correlating misconfigurations across layers
- identifying potential attack paths
This shifts security from isolated checks to system-level analysis, where the focus is not only on individual configurations but on how they interact within the broader architecture.
Integrating CSPM into DevSecOps Workflows
Shifting Security Left in Infrastructure Pipelines
As cloud environments become fully programmable, security must move closer to where infrastructure is defined and deployed. This shift—commonly referred to as “shift-left security”—is essential for maintaining control in systems that evolve continuously.
Cloud Security Posture Management plays a central role in this transition by integrating directly into infrastructure as code workflows. Instead of detecting misconfigurations after deployment, Cloud Security Posture Management enables teams to validate configurations before resources are created.
This approach allows security to become part of the development lifecycle rather than a separate validation phase. Infrastructure definitions can be evaluated as early as the pull request stage, ensuring that issues are identified before they propagate across environments.
This is typically implemented by embedding Cloud Security Posture Management checks into:
- Terraform and CloudFormation pipelines
- pull request validation processes
- CI/CD workflows
By enforcing security at this stage, organizations reduce remediation costs and prevent insecure configurations from reaching production.
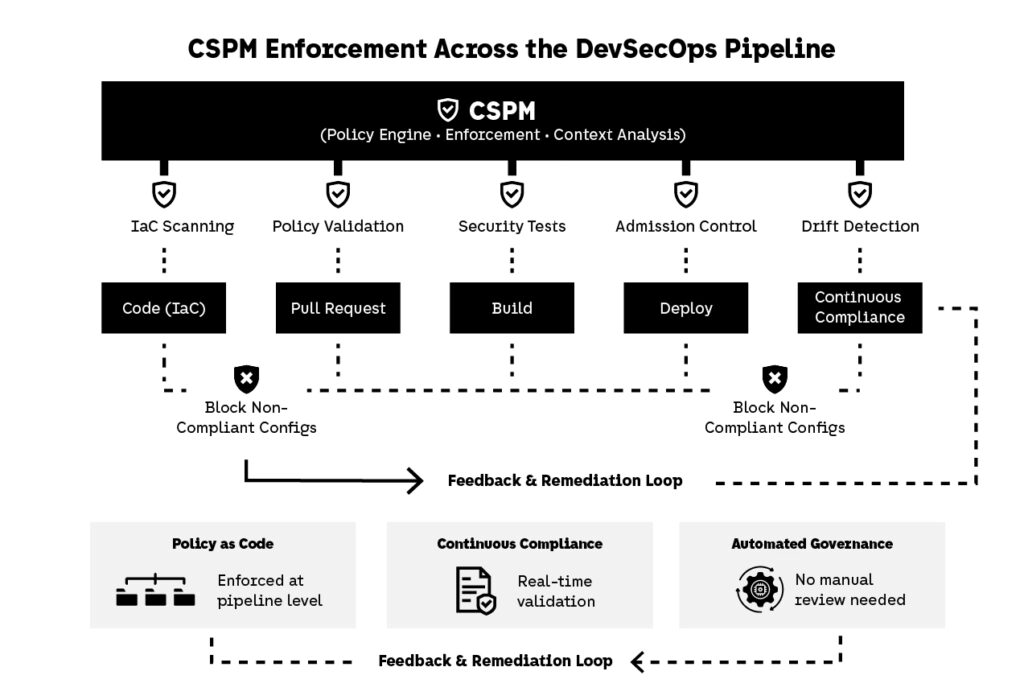
Policy as Code and Automated Governance
To scale security effectively, policies must be defined in a way that is enforceable by systems rather than individuals. This leads to the adoption of policy-as-code, where security rules are expressed programmatically and applied automatically across environments.
Cloud Security Posture Management integrates with policy-as-code frameworks to enforce governance consistently. Policies can define what constitutes a compliant configuration, and infrastructure that does not meet these requirements can be automatically rejected.
This enables organizations to:
- enforce compliance rules during deployment
- block non-compliant configurations before execution
- maintain consistency across teams and environments
HashiCorp provides guidance on implementing policy controls in infrastructure workflows.
In this model, Cloud Security Posture Management transforms security from a manual review process into a system constraint. Infrastructure must comply with defined policies to be deployed, eliminating ambiguity and reducing reliance on human intervention.
Continuous Compliance and Real-Time Validation
In dynamic cloud environments, compliance cannot be treated as a periodic activity. Systems change too frequently for point-in-time audits to provide meaningful assurance.
Cloud Security Posture Management enables continuous compliance by monitoring infrastructure in real time and validating configurations against regulatory and internal standards.
This allows organizations to:
- detect compliance violations as they occur
- maintain audit-ready environments at all times
- generate evidence automatically for regulatory requirements
Rather than preparing for audits retroactively, teams operate within environments that are continuously aligned with compliance expectations.
This shift reduces operational overhead and improves confidence in system integrity.
Bridging Development, Security, and Platform Engineering
One of the most significant challenges in modern cloud environments is the disconnect between teams responsible for building, securing, and operating systems.
Cloud Security Posture Management helps bridge this gap by providing a shared layer of visibility and enforcement. It enables:
- security teams to define policies
- development teams to implement infrastructure
- platform teams to enforce governance at scale
By exposing consistent insights across all stakeholders, Cloud Security Posture Management reduces friction and aligns decision-making.
Issues are no longer isolated within specific teams. Instead, they are surfaced within a shared system context, where responsibilities are clearer and remediation becomes more efficient.
This alignment is critical in high-velocity environments, where delays in communication can translate directly into increased risk.
Common Cloud Security Posture Management Failure Modes
Treating Cloud Security Posture Management as a Standalone Tool
A common mistake organizations make is approaching Cloud Security Posture Management as a tool that operates independently from the systems it is meant to secure.
In this model, Cloud Security Posture Management is deployed to scan environments and generate alerts, but it remains disconnected from development workflows, deployment pipelines, and operational processes.
This creates a structural gap between detection and action. Issues are identified, but remediation depends on manual intervention, which introduces delays, inconsistency, and ultimately risk accumulation.
As cloud environments scale, this approach becomes increasingly ineffective. Findings grow faster than teams can resolve them, leading to a backlog of unresolved misconfigurations.
To be effective, Cloud Security Posture Management must be embedded into the system itself—integrated into how infrastructure is defined, deployed, and maintained—rather than positioned as an external observer.
Alert Fatigue and Lack of Context
Another frequent failure mode is the overproduction of alerts without sufficient context.
Basic implementations of Cloud Security Posture Management often rely on rule-based checks that produce binary outcomes:
- compliant
- non-compliant
While simple, this approach does not reflect actual risk.
For example:
- a publicly exposed resource may be acceptable depending on its purpose
- a seemingly minor configuration issue may become critical when combined with identity permissions or data exposure
Without context, teams are forced to treat all alerts equally. This leads to alert fatigue, where high-risk issues are overlooked because they are buried among low-impact findings.
Modern approaches to Cloud Security Posture Management address this by incorporating:
- risk prioritization
- resource relationships
- exposure analysis
This enables teams to focus on meaningful risk rather than reacting to every deviation.
Lack of Ownership and Accountability
Security findings only have value if they lead to action. In many organizations, Cloud Security Posture Management surfaces issues without clearly identifying who is responsible for resolving them.
This is particularly problematic in distributed environments, where:
- infrastructure is shared across teams
- ownership is not clearly defined
- responsibilities are fragmented
As a result, issues persist—not because they are ignored, but because they lack clear accountability.
To address this, Cloud Security Posture Management must align with organizational structures. This includes:
- mapping resources to teams
- enforcing consistent tagging strategies
- integrating with ticketing and incident management systems
By linking findings to ownership, organizations can ensure that identified risks are systematically resolved.
Over-Reliance on Compliance as a Proxy for Security
Compliance frameworks provide valuable guidance, but they are not a complete representation of security.
Systems can meet compliance requirements while still being vulnerable due to:
- overly permissive access controls
- unintended interactions between services
- exposure paths created by system relationships
Cloud Security Posture Management should not be limited to compliance validation. It must also incorporate system-level analysis that reflects how components interact in real environments.
This includes:
- identifying compound risks across services
- analyzing potential attack paths
- understanding how configurations behave collectively
In this context, compliance should be treated as a baseline—not as a guarantee of security.
What Cloud Security Posture Management Changes for Cloud Security in 2026
From Reactive Security to Continuous Validation
Cloud Security Posture Management fundamentally changes how cloud security is approached by shifting the focus from reactive detection to continuous validation.
Traditional security models are built around identifying and responding to incidents after they occur. In cloud-native environments, this model breaks down due to the speed and scale at which infrastructure evolves.
Cloud Security Posture Management introduces a system where infrastructure is continuously evaluated against defined security expectations. Instead of relying on periodic audits or manual reviews, organizations maintain a real-time understanding of their security posture.
This shift reduces the window between misconfiguration and detection, limiting the opportunity for exploitation and improving overall system resilience.
Security as a System Property, Not a Layer
One of the most significant changes introduced by Cloud Security Posture Management is the repositioning of security within the architecture.
Rather than being applied as an external layer, security becomes an inherent property of the system itself.
This is achieved by embedding Cloud Security Posture Management into:
- infrastructure as code workflows
- deployment pipelines
- runtime monitoring systems
In this model, security is not something added after deployment—it is enforced throughout the lifecycle of the system.
This aligns with broader trends in cloud-native engineering, where systems are designed to be:
- automated
- observable
- continuously validated
Managing Complexity Without Losing Control
As organizations scale across multi-cloud environments and distributed systems, complexity increases rapidly.
Without a structured approach, this complexity leads to:
- inconsistent configurations
- fragmented visibility
- increased risk exposure
Cloud Security Posture Management provides a mechanism to manage this complexity by:
- centralizing visibility
- standardizing policy enforcement
- correlating risk across systems
This allows organizations to scale infrastructure without losing control over their security posture.
The Shift Toward Architecture-Level Security
Cloud Security Posture Management represents a broader transition toward architecture-level security.
Instead of focusing on individual components or isolated controls, organizations must consider how systems behave as a whole.
Security decisions are no longer limited to:
- configuring a single resource
- applying a specific rule
They involve understanding:
- relationships between services
- identity and access flows
- data exposure paths across environments
Cloud Security Posture Management enables this perspective by providing the context needed to evaluate systems holistically.
What This Means Going Forward
In 2026, Cloud Security Posture Management is no longer an optional capability. It is a foundational component of modern cloud architecture.
Organizations that adopt this model gain the ability to:
- detect and resolve misconfigurations early
- enforce consistent security policies across environments
- maintain visibility as systems evolve
Those that rely on fragmented tooling and manual processes will struggle to keep pace with the scale and complexity of cloud-native systems.
Cloud Security Posture Management enables a shift from managing individual risks to managing systems as a whole—ensuring that security evolves alongside infrastructure rather than reacting to it.


